Introduction To Game Theory And Mechanism Design Iitk
eMasters Highlights
About eMasters in Cyber Security
With the growing number of cyber attacks on important information systems, critical infrastructures, personal devices, etc. there is an urgent and massive need for cyber security professionals with the right capabilities. Our comprehensive IIT Kanpur eMasters program will train you in the latest tools and technologies, techniques, and concepts in Cyber Security. Prepare yourself to successfully navigate the changing landscape of Cyber Security.

Faculty
Learn from the experts working at the forefront of cutting-edge research and technology in Cyber Security.
-
 Manindra Agrawal
Manindra Agrawal
B.Tech. and Ph.D. in Computer Science and Engineering from IIT Kanpur
Computational Complexity Theory, Security, Theoretical Computer Science and Algorithms

-
 Sandeep K. Shukla
Sandeep K. Shukla
Ph.D., State University of New York at Albany
M.S., State University of New York at Albany
Application of Formal Methods to Embedded and Cyberphysical Systems and Embedded Computing

-
 Urbi Chatterjee
Urbi Chatterjee
M.Tech in Computer Applications, Indian School of Mines, Dhanbad
Ph. D., IIT Kharagpur
Hardware Security, Physically Unclonable Functions, Secure Authentication Protocols Design and Internet of Things Security

-
 Nitin Saxena
Nitin Saxena
B.Tech. and Ph.D. in Computer Science and Engineering from IIT Kanpur
Computational Complexity Theory, Algebra, Algebraic Geometry, Theoretical Computer Science and Algorithms

-
 Indranil Saha
Indranil Saha
Ph.D. in Computer Science, University of California, Los Angeles
Embedded and Cyber-Physical Systems, Robotics and Automation, Artificial Intelligence and Formal Methods

-
 Swaprava Nath
Swaprava Nath
Ph.D. in Computer Science, IISc, Bangalore
M.E. in Telecommunication, IISc, Bangalore
Artificial Intelligence, Multi Agent Systems, Game Theory, Mechanism Design, Computational Social Choice and Crowdsourcing

-
 Debadatta Mishra
Debadatta Mishra
Ph.D., IIT Bombay
Operating Systems, Virtualization and Cloud Computing and Computer Networks

-
 Shubham Sahay
Shubham Sahay
Ph.D. in Electrical Engineering, IIT Delhi
B.Tech in Electronics Engineering, IIT BHU
Nanoscale Device Design and Modeling, Neuromorphic Computing, Hardware Security

Curriculum
A well-researched real-world curriculum by IIT Kanpur's subject matter experts that fosters hands-on learning and helps you master the desired capabilities by combining deep formal rigor and an intense practical approach.
Modules
Immersive Learning Format
Outcomes
Eligibility
Program Fee
| Details | Payment Schedule | Amount |
|---|---|---|
| Program Registration Fee To Block Your Seat | Within 1 Week of Selection | ₹40,000 |
| Program Registration Fee To Complete Your Registration | As per the Selection Letter | ₹1,60,000 |
| Quarter Registration Fee For 1st Quarter | As per the Selection Letter | ₹15,000 Per Quarter |
| Module Fee For 1st Quarter Modules | As per the Selection Letter | ₹45,000 Per Module |
![]() Exclusive ₹2,00,000 Scholarship for January 2022 Batch: Adjust your Scholarship against the fee payable from the 4th Quarter.
Exclusive ₹2,00,000 Scholarship for January 2022 Batch: Adjust your Scholarship against the fee payable from the 4th Quarter.
Frequently Asked Questions
Core Modules
- Introduction to Cryptography
The module covers the basics of finite field Arithmetic, private and public-key cryptography, existing cryptosystems and their security, Cryptanalysis of existing systems and more. - Operating System Principles
The module covers the computer organization interface, the concept of a process, threads, scheduling, process synchronization, deadlocks, memory management, and more. - Computer Networking I
The module covers the introduction, history, and development of computer networks, networks topologies, various aspects of layering and protocols, physical layer, MAC layer, data link layer, and more. - Introduction to Application Security, Mobile Security, and Critical Infrastructure Security
The module covers various aspects of Security in Mobile Platforms, Application Security, and Issues in Critical Infrastructure and SCADA Security. - Introduction to Linear Algebra
The module covers vector spaces, examples, Rn, Cn; subspaces, linear independence, dependence and dimension, linear transformations, matrices, matrix algebra, determinants, properties of matrices and determinants, systems of linear equations, and more. - Machine Learning for Cyber Security
The module covers an introduction to data classification, Supervised vs. Unsupervised Learning, Linear Regression, Multivariate Regression., Logistic Regression, Hypothesis Testing, Maximum Likelihood Estimation, Bayesian Classification, Model Selection, Regularization, Generalization, Cross Validation and more. - Introduction to Web Security, Network Security and Defenses
The module covers Security Issues in TCP/IP, Wireless Security, Network Defense tools, DNSSec, NSec3, Distributed Firewalls, Intrusion Detection tools, Threat Models, Denial of Service Attacks, DOS-proof network architecture, Security architecture of World Wide Web, Security Architecture of Web Servers, and Web Clients and more. - Advanced Topics in Cryptography
The module covers zero-knowledge protocols, one-way functions, advanced protocols for different applications, network, and system-level security issues, post- quantum Cryptography, and more. - Embedded and Cyber Physical Systems
The module covers the modeling, implementation, and verification issues related to developing a cyber-physical system. In addition, through the discussion of implementing an embedded control system, the module will cover the basic design principles of an embedded system. - Introduction to Hardware Security
The module provides an in-depth understanding of Internet of Things (IoT) ecosystem and security vulnerabilities, attacks on cyber-physical systems, reverse engineering, side-channel attacks, intellectual property (IP) piracy, Hardware Trojan, electronic counterfeiting, Physical Unclonable Function (PUF) and more. - Advanced Critical Infrastructure Security
The module covers Stuxnet worm and its aftereffects in the Critical Infrastructure security, Game Theory and other analytical modeling of the security problems of critical infrastructures, security of the Networked Infrastructure, event monitoring, Event Correlation, and Situational Awareness, vulnerability Database and its importance and more. - Cyber Laws, Case Studies and Trends
The module covers the importance of Cyber Laws and Extant Cyber Laws in India, a comparison between Cyber Law regimes in India and US/Europe, Cyber Security Regulation, Standards, Policies, Architecture, and Compliance, Compliance Automation and Case Studies from the field.
Quarter 1
- Introduction to Cryptography
- Operating System Principles
- Introduction to Application Security, Mobile Security and Critical Infrastructure Security
Quarter 2
- Computer Networking
- Introduction to linear Algebra
- Introduction to web security, Network Security and Defenses
Quarter 3
- Machine Learning for Cyber Security
- Introduction to Hardware Security
- Embedded and Cyber Physical Systems and loT Security
Quarter 4
- Advanced Topics in Cryptography
- Advanced Critical Infrastructure Security
- Cyber laws, Case Studies and Trends
About IIT Kanpur
Established in 1959 by the Government of India, Indian Institute of Technology Kanpur (IIT Kanpur) is a globally acclaimed university for world-class education and research in science, engineering, management and humanities. We aim to provide leadership in technological innovation for the growth of India.


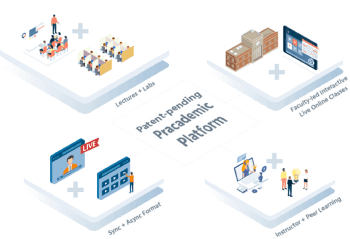
State-of-the-Art Digital Learning Platform
The eMasters Program by IIT Kanpur will be delivered on iPearl.ai, a State-of-the-Art digital learning platform, powered by TalentSprint. iPearl.ai, highly rated for its user experience, is a direct-to-device platform that works seamlessly on any internet-connected device and provides a single-sign on experience for all your learning needs including recorded videos, reading material, live interactive sessions, assignments, quizzes, discussion forums, virtual lounges and more.
Introduction To Game Theory And Mechanism Design Iitk
Source: https://emasters.iitk.ac.in/cybersecurity
Posted by: gardnerthertat.blogspot.com

0 Response to "Introduction To Game Theory And Mechanism Design Iitk"
Post a Comment